Robust and Efficient Privacy Preservation in Industrial IoT via correlation completion and tracking
Abstract
The Industrial IoT (IIoT) is a key element of Industry 4.0, bringing together modern sensor technology, fog - cloud computing platforms, and artificial intelligence (AI) to create smart, self-optimizing industrial equipment and facilities. Though, the scale and sensitivity degree of information con- tinuously increases, giving rise to serious privacy concerns. In this work we address the problem of efficiently and effectively tracking the structure of multivariate streams recorded in a network of IIoT devices. The time varying correlation data values are used to add noise which maximally preserves privacy, in the sense that it is very hard to be removed. T o improve communication efficiency between connected IoT devices, we exploit low rank properties of the correlation matrices, and track the essential correlations from a small subset of correlation values estimated by a subset of network nodes. Extensive simulation studies, validate the correctness, efficiency, and effectiveness of our approach in terms of computational complexity, transmission energy efficiency and privacy preservation. I.
Key Contributions
- Proposing a privacy-preserving method for reconstructing the PCA subspace from a subset of correlation values, ensuring that the correlation matrices cannot reveal sensitive information.
- Introducing an adaptive matrix completion approach that solves a rank-one completion problem iteratively, addressing the issue of missing entries in distributed IIoT networks.
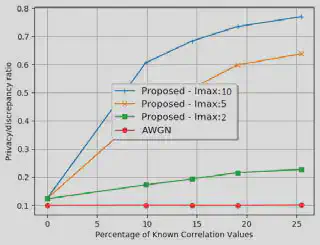
- Demonstrating through extensive simulations that the proposed approach improves privacy preservation, computational efficiency, and robustness against node and link failures.
Results & Insights